Disclaimer:
The RSS blog posts featured on our website are external articles imported through an automated process. We do not verify the accuracy or completeness of the information contained in these posts. The views and opinions expressed in these articles are those of the authors and do not necessarily reflect our own. We are not responsible for any errors, omissions, or misstatements that may appear in these posts. Readers are advised to independently verify any information before relying on it.
If you find any information that you believe to be dangerous, harmful, inaccurate, or in violation of GDPR or other laws, please contact us immediately, and we will take steps to remove it.
A hacker creates a million virtual servers to mine cryptocurrency illegally
Cyber Security Blogs This week, a 29-year-old man from Ukraine was taken into custody for creating one million virtual servers through the use of compromised accounts, which were then used to mine $2 million in cryptocurrency. According to what Europol announced, the suspect is thought to be the brains behind a massive cryptojacking operation that
- Published in RSS blog posts
A Magic Keyboard Bug That Allowed Bluetooth Traffic Monitoring Was Fixed By Apple
Cyber Security Blogs A recently discovered Bluetooth keyboard injection issue, identified as CVE-2024-0230, was fixed by Apple with the release of Magic Keyboard Firmware Update 2.0.6. An attacker with physical access to the accessory could use this flaw, which is a session management issue, to extract the Bluetooth pairing key and eavesdrop on Bluetooth conversations.
- Published in RSS blog posts
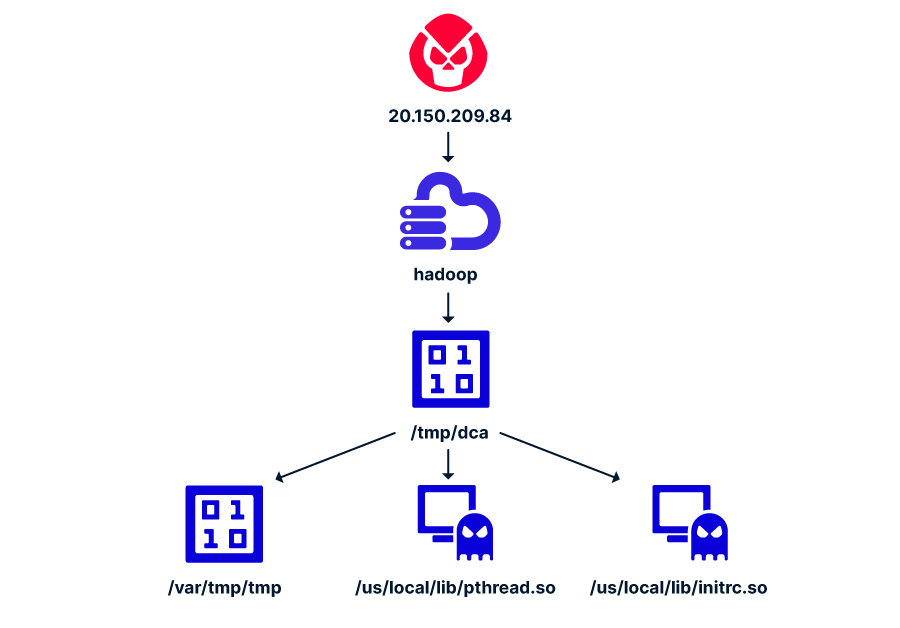
Attackers target Apache Hadoop and Flink to deliver cryptominers
Cyber Security BlogsResearchers devised a new attack that exploits misconfigurations in Apache Hadoop and Flink to deploy cryptocurrency miners. Cybersecurity researchers from cyber security firm Aqua have uncovered a new attack targeting Apache Hadoop and Flink applications. The attacks exploit misconfigurations in Apache Hadoop and Flink to deploy cryptocurrency cryptocurrency miners. The researchers reported that
- Published in RSS blog posts
TCE Exclusive: McDonald’s Data Breach 2024, a Continuation of Cybersecurity Dilemmas
Cyber Security Blogs In a developing story that underscores the persistent challenges of cybersecurity in the corporate world, an alleged new McDonald’s data breach was reported on Sunday, January 13, 2024. The information about this latest McDonald’s data breach surfaced on BreachForums, where a user named ‘euphoria’ claimed to have accessed a significant volume of
- Published in RSS blog posts
Tura Scandinavia AB Encounters Another Cyberattack Following intrusion in December
Cyber Security Blogs Tura Scandinavia AB allegedly finds itself targeted by the LockBit ransomware group, marking another episode in the company’s history of cybersecurity challenges. This cyberattack on Tura Scandinavia AB, accompanied by a now-closed deadline date, was posted on the dark web where the threat actor, the LockBit ransomware group, posted its claims of
- Published in RSS blog posts
Juniper fixes critical RCE in its SRX firewalls and EX switches (CVE-2024-21591)
Cyber Security Blogs Juniper Networks has fixed a critical pre-authentication remote code execution (RCE) vulnerability (CVE-2024-21591) in Junos OS on SRX firewalls and EX switches. About CVE-2024-21591 CVE-2024-21591 is an out-of-bounds write vulnerability that could allow an unauthenticated, network-based threat actor to carry out a denial-of service (DoS) attack, an RCE attack, or gain root
- Published in RSS blog posts
Flipping the BEC funnel: Phishing in the age of GenAI
Cyber Security Blogs For years, phishing was just a numbers game: A malicious actor would slap together an extremely generic (and usually poorly-written) email and fire it out to thousands of recipients in the hope that a few might take the bait. Over time, however, as spam filters and other email security tools became increasingly
- Published in RSS blog posts
NoName Targets Multiple Websites in Lithuania, Blames it for Aiding Ukraine
Cyber Security Blogs Several prominent organizations in Lithuania, including Compensa Vienna Insurance Group, If Insurance, Lithuanian Roads Association, AD REM, INIT, and Balticum, have allegedly fallen victim to the NoName attack. The threat actors, identified as the NoName ransomware group, have been actively sharing posts detailing the impact of the cyberattack on Lithuania websites. The
- Published in RSS blog posts
Preventing insider access from leaking to malicious actors
Cyber Security Blogs In this Help Net Security video, John Morello, CTO of Gutsy, discusses the often-overlooked aspect of cybersecurity – the offboarding process. He outlines the real-world implications and potential impact on an organization’s security posture if off-boarding isn’t handled thoroughly. The post Preventing insider access from leaking to malicious actors appeared first on
- Published in RSS blog posts
Adalanche: Open-source Active Directory ACL visualizer, explorer
Cyber Security Blogs Adalanche provides immediate insights into the permissions of users and groups within an Active Directory. It’s an effective open-source tool for visualizing and investigating potential account, machine, or domain takeovers. Additionally, it helps identify and display any misconfigurations. What unique features make Adalanche stand out? “The best feature is the low user
- Published in RSS blog posts