Disclaimer:
The RSS blog posts featured on our website are external articles imported through an automated process. We do not verify the accuracy or completeness of the information contained in these posts. The views and opinions expressed in these articles are those of the authors and do not necessarily reflect our own. We are not responsible for any errors, omissions, or misstatements that may appear in these posts. Readers are advised to independently verify any information before relying on it.
If you find any information that you believe to be dangerous, harmful, inaccurate, or in violation of GDPR or other laws, please contact us immediately, and we will take steps to remove it.
How to be effective working from home
Cyber Security Blogs Many people struggle to stay focused as part of a remote workforce. When you are physically in the office you have nothing to do but work and your only distraction is typically the internet and your co-workers. When you’re working from home you can have several things that are distracting you, this
- Published in RSS blog posts
How to do digital marketing for a cybersecurity company
Cyber Security Blogs Every company that needs to get clients can benefit from digital marketing. Digital marketing is everything that you do online to promote your products, services or build your online brand. One key component of being good at digital marketing is understanding the temperament of the industry you are dealing with; every industry
- Published in RSS blog posts
What is an Indicator of Compromise
Cyber Security Blogs An Indicator of Compromise (IOC) is a forensic artifact that identifies a potentially malicious activity on a system or network. IOCs are important for both prevention and detection of cyber threats. By inputting IOCs of new cyber threats into software products they can block any processes that match these IOCs and therefore
- Published in RSS blog posts
Best VPNs for online privacy
Cyber Security Blogs As we browse the internet we create tons of information that can be stolen and used against us for fraud or other crimes. Companies known as data brokers have a vested interest in collecting this information and selling it to other parties for a profit. It’s important that we take precautions to
- Published in RSS blog posts
Weekly Update 382
Cyber Security Blogs Geez it’s nice to be back in Oslo! This city has such a special place in my heart for so many reasons, not least of which by virtue of being Charlotte’s home town we have so many friends and family here. Add in NDC Security this week with so many more mutual
- Published in RSS blog posts
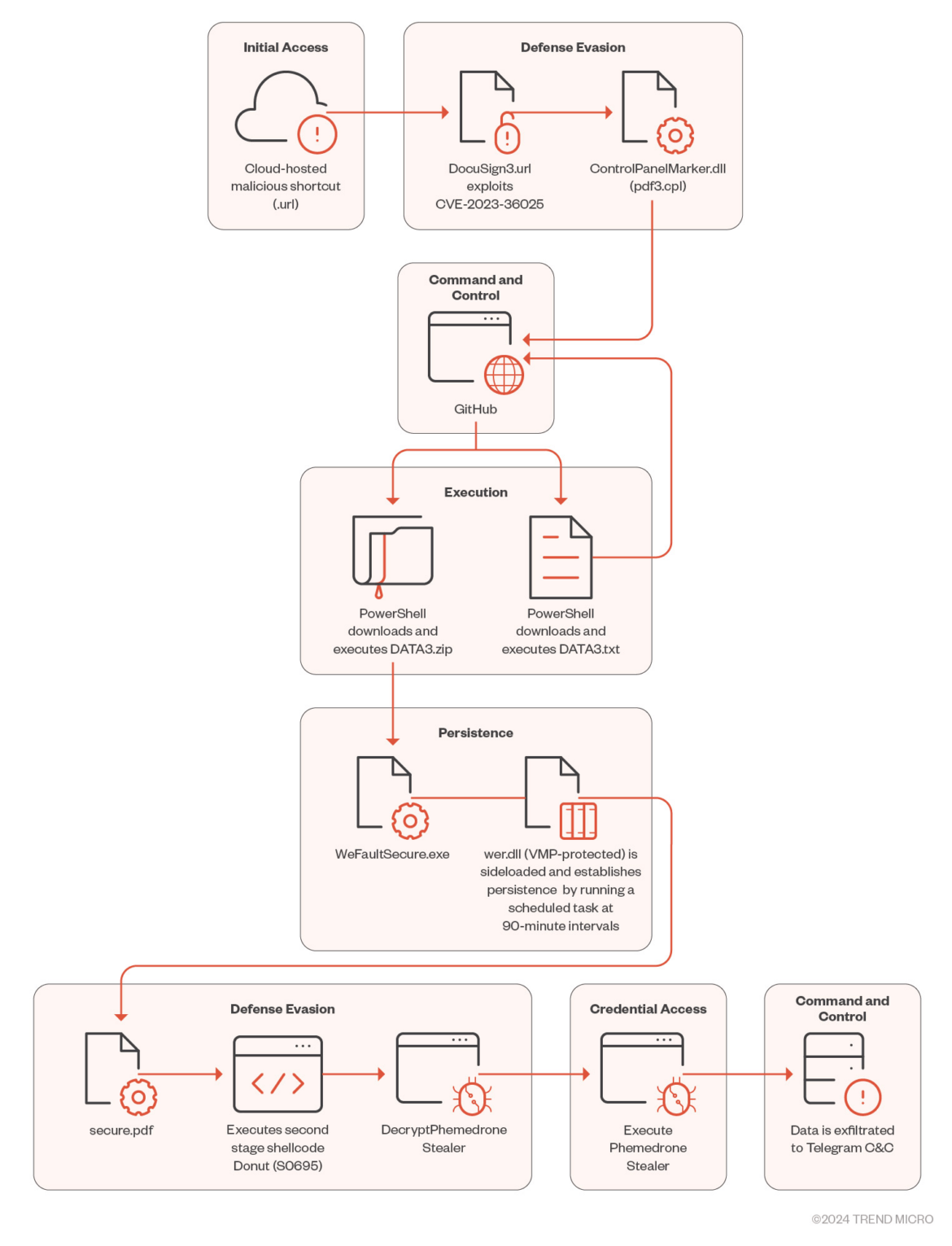
Phemedrone info stealer campaign exploits Windows smartScreen bypass
Cyber Security BlogsThreat actors exploit a recent Windows SmartScreen bypass flaw CVE-2023-36025 to deliver the Phemedrone info stealer. Trend Micro researchers uncovered a malware campaign exploiting the vulnerability CVE-2023-36025 (CVSS score 8.8) to deploy a previously unknown strain of the malware dubbed Phemedrone Stealer. The vulnerability was addressed by Microsoft with the release of Patch Tuesday security
- Published in RSS blog posts
Akeyless Universal Secrets Connector: A Secrets Manager of Managers
Cyber Security BlogsDiscover the power of External Secrets Manager with Akeyless. Simplify secrets management across multiple platforms and clouds, centralize control, enhance visibility, and ensure compliance. Read More
- Published in RSS blog posts
How Akeyless Universal Secrets Connector is Revolutionizing Multi-Cloud Environments
Cyber Security BlogsDiscover Akeyless USC, the unified solution for centralizing and securing secrets in today’s multi-cloud environment, enhancing compliance and operational efficiency. Read More
- Published in RSS blog posts
Windows SmartScreen bug exploited to deliver powerful info-stealer (CVE-2023-36025)
Cyber Security Blogs A vulnerability (CVE-2023-36025) that Microsoft fixed in November 2023 continues to be exploited by malware peddlers: this time around, the delivered threat is a variant of the Phemedrone Stealer. About the malware Phemedrone Stealer is a piece of malware written in C#, with no dependencies. It’s capable of: Collecting system information (hardware,
- Published in RSS blog posts
MLK Day: Here’s What Every CISO Can Learn from Martin Luther King Jr.
Cyber Security Blogs MLK Day 2024: As the world commemorates Martin Luther King Jr. Day on January 15, 2024, it’s an opportune time to reflect on the enduring impact of Dr. King’s leadership. His qualities and vision not only shaped the civil rights movement but also offered timeless insights for today’s leaders, particularly Chief Information
- Published in RSS blog posts