Cyber Security BlogsResearchers devised a new attack that exploits misconfigurations in Apache Hadoop and Flink to deploy cryptocurrency miners.
Cybersecurity researchers from cyber security firm Aqua have uncovered a new attack targeting Apache Hadoop and Flink applications. The attacks exploit misconfigurations in Apache Hadoop and Flink to deploy cryptocurrency cryptocurrency miners.
The researchers reported that the attack is particularly intriguing because threat actors use packers and rootkits to conceal the malware.
Apache Hadoop is an open-source software framework designed for the distributed storage and processing of large sets of data using a cluster of commodity hardware. It is part of the Apache Software Foundation’s efforts and is widely used for handling big data and performing parallel processing tasks.
Apache Flink is an open-source, unified stream-processing and batch-processing framework developed by the Apache Software Foundation.
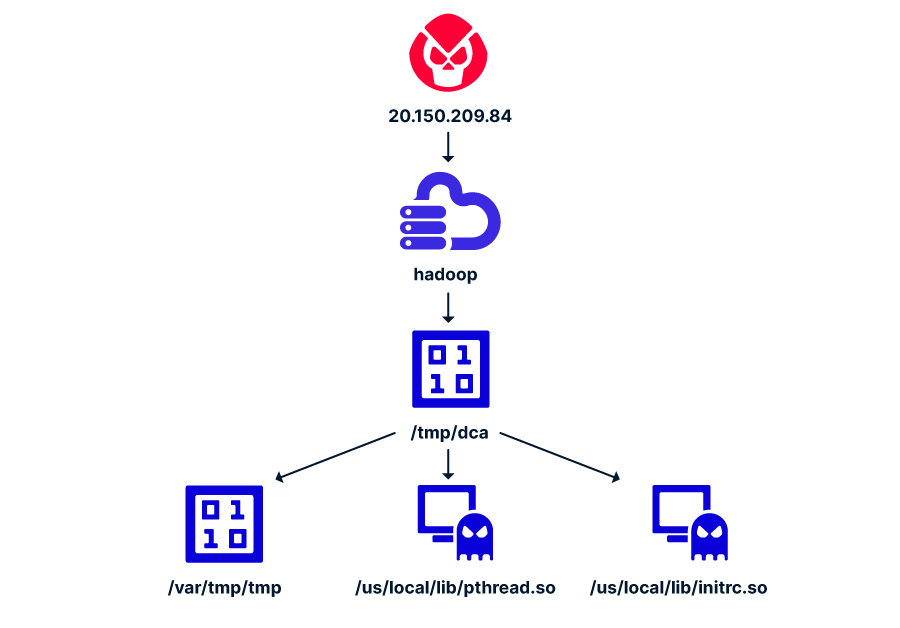
The attack is very simple, attackers exploit a misconfiguration of the ResourceManager of the YARN in Hadoop to drop and executed the binary dca which downloads two other binaries (rootkits) and writes to disk a Monero cryptominer.
The attacker sends an unauthenticated request to deploy a new application, then he attempts
to to run a remote code by sending a POST request to the YARN, requesting to launch the new application with the attacker’s command.
The misconfiguration allows an unauthenticated, remote threat actor to execute arbitrary code through a specially crafted HTTP request. An attacker can execute arbitrary code depending on the privileges of the user on the node where the code is executed.
The attack against the Apache Flink is quite similar and exploits a misconfiguration that allows a remote, unauthenticated attacker to achieve code execution.
“The attack employs sophisticated evasion techniques, including the use of packed ELF binaries and rootkits that are undetected by regular security solutions. The malware deletes contents of specific directories and modifies system configurations to evade detection.” states the report. “Persistence is achieved by manipulating cron jobs to download and execute a script that deploys the ‘dca’ binary. The infrastructure used by the attackers includes specific IP addresses and domains.”
The report also includes Indications of Compromise (IoCs) for this attack.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Apache Hadoop)



