Gartner’s Verdict: Trend Micro Dominates the Endpoint Security Landscape
Cyber Security Blogs Gartner’s Verdict: Trend Micro Dominates the Endpoint Security Landscape | OluKaii (I-SOS) HyBrid i•CyberTech Specialist Group by Quinline Olukoya Photo by Junior Teixeira on Pexels.com The World of Cybersecurity is ever-evolving and complex, and at its heart lies the concept of endpoint security. Endpoint security refers to the practice of securing endpoints
- Published in RSS blog posts
Privacy Law Compliance: Managing Online Tracking (Ad Tech) Vendors
Cyber Security Blogs TrustArc privacy expert Andrew Scott shares strategies for navigating online tracking vendor relationships under privacy laws such as CCPA/CPRA. The post Privacy Law Compliance: Managing Online Tracking (Ad Tech) Vendors appeared first on TrustArc Privacy Blog. Read More
- Published in RSS blog posts
Cyber Security & Cloud Congress Returns To Santa Clara – What To Expect
Cyber Security Blogs Cyber Security & Cloud Congress 2024, is an esteemed assembly of more than 7,000 professionals in the Cyber Security & Cloud field. The event is scheduled to occur on June 5-6, 2024, at the Santa Clara Convention Center. Envisioned as one of the most extensive conferences and exhibitions of its category
- Published in RSS blog posts
PCI DSS Requirement 2 – Changes from v3.2.1 to v4.0 Explained
Cyber Security Blogs In our last discussion, we explored the evolution of Requirement 1 in the transition from PCI DSS v3.2.1 to v4.0, with a particular emphasis on the move towards ‘network security controls’. As we continue our exploration of the updated PCI DSS v4.0, today’s focus will be on the transformations in Requirement 2.
- Published in RSS blog posts
Incogni Vs DeleteMe – Which Is Better?
Cyber Security Blogs Read on for the Incogni vs DeleteMe comparison. Your data on data brokers and people search websites is a huge risk. Anyone can get hold of it and do anything with it. For example, hackers can steal your identity and carry out malicious activities. But there’s good news! You can easily remove
- Published in RSS blog posts
Is Surfshark One Worth It? [Honest ANSWER]
Cyber Security Blogs Is Surfshark One Worth It? Read on to find out. The menace that is online crime continues to persist, taking different forms. According to statistics, coordinated cybersecurity attacks affect more than 3.8 million records every day. Such a high number is alarming, and as an internet user, it calls for attention to
- Published in RSS blog posts
Virtual kidnapping: How to see through this terrifying scam
Cyber Security BlogsPhone fraud takes a frightening twist as fraudsters can tap into AI to cause serious emotional and financial damage to the victims Read More
- Published in RSS blog posts
Is Temu safe? What to know before you ‘shop like a billionaire’
Cyber Security BlogsHere are some scams you may encounter on the shopping juggernaut, plus a few simple steps you can take to help safeguard your data while bagging that irresistible deal Read More
- Published in RSS blog posts
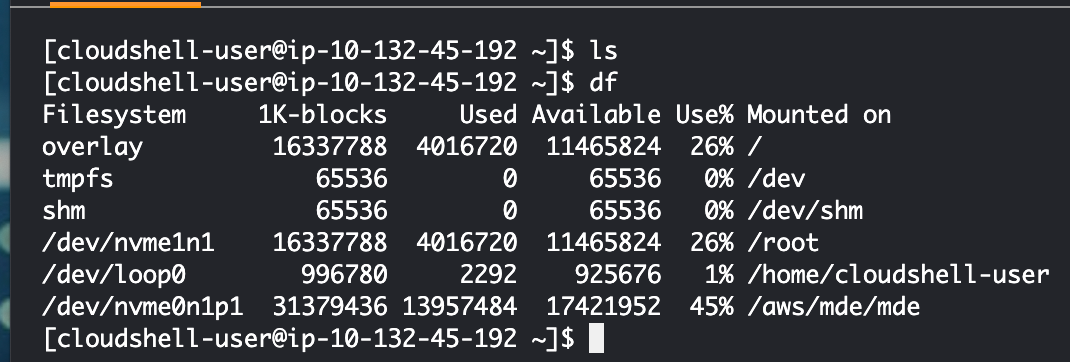
A Docker Container In CloudShell
Cyber Security Blogs ACM.435 Building and running containers in AWS CloudShell Read More
- Published in RSS blog posts
VF Corp December data breach impacts 35 million customers
Cyber Security BlogsAmerican global apparel and footwear company VF Corp revealed that the December data breach impacted 35.5 million customers. VF Corporation is an American global apparel and footwear company that owns 13 brands. In 2015, the company controlled 55% of the U.S. backpack market with the JanSport, Dickies, Eastpak, Timberland, Smartwool, Vans, and The North Face brands. In December
- Published in RSS blog posts