Disclaimer:
The RSS blog posts featured on our website are external articles imported through an automated process. We do not verify the accuracy or completeness of the information contained in these posts. The views and opinions expressed in these articles are those of the authors and do not necessarily reflect our own. We are not responsible for any errors, omissions, or misstatements that may appear in these posts. Readers are advised to independently verify any information before relying on it.
If you find any information that you believe to be dangerous, harmful, inaccurate, or in violation of GDPR or other laws, please contact us immediately, and we will take steps to remove it.
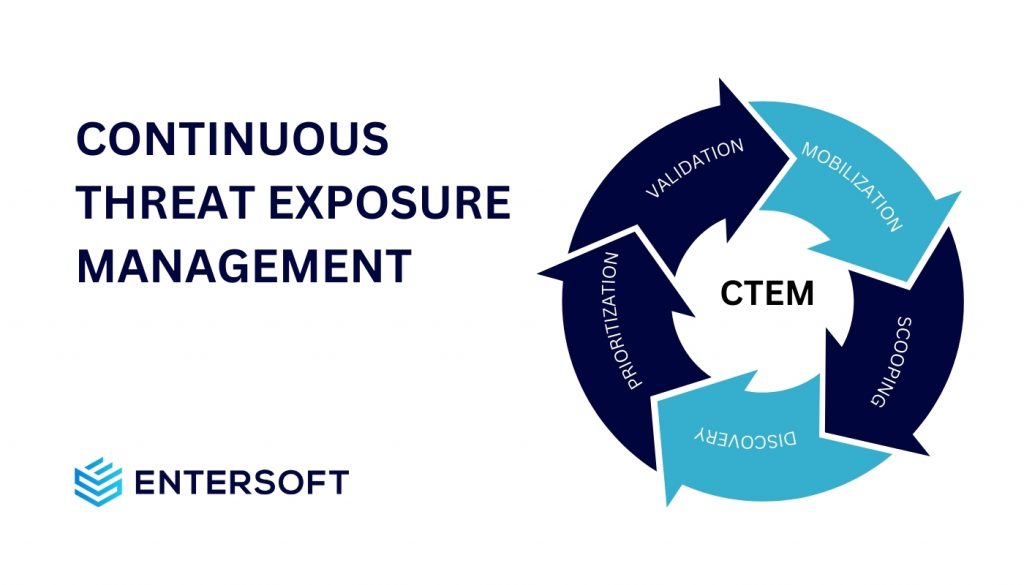
Harnessing Continuous Threat Exposure Management (CTEM) for Business Security
Cyber Security Blogs The Post Harnessing Continuous Threat Exposure Management (CTEM) for Business Security Appeared on first on Blog – In the dynamic world of cybersecurity, Continuous Threat Exposure Management (CTEM) has emerged as a crucial approach for organizations seeking to safeguard their digital assets and operations. The rise of CTEM is not just a
- Published in RSS blog posts
tunnel.googlezip.net?
Cyber Security BlogsThis doesn’t look good — and I don’t think it is a “crawler” If this is legitimate, it is not a good name. Apparently others are having problems with this domain: Best way to stop tunnel.google.zip and excessive crawling spam – Google Search Central Community If it is actually a “crawler” then why is it trying to
- Published in RSS blog posts
Dealing with Million Unpatched Vulnerabilities. Where do we start?
Cyber Security Blogs While the digital realm brings convenience and connectivity, it also introduces a bunch of vulnerabilities that can compromise the security and integrity of systems. As the number of unpatched vulnerabilities continues to rise, IT Security teams find themselves struggling with the task of securing their digital assets. With millions of vulnerabilities to
- Published in RSS blog posts
Proactive Vulnerability Mitigation: Staying Ahead of Cyber Threats
Cyber Security Blogs Companies are taking proactive steps to address vulnerabilities before their security team find and resolve them. While this approach is necessary and effective to a certain extent, it carries the risk of delayed responses, leaving systems exposed to potential threats. According to Check Point Research, Global Cyberattacks have increased by 38% in
- Published in RSS blog posts
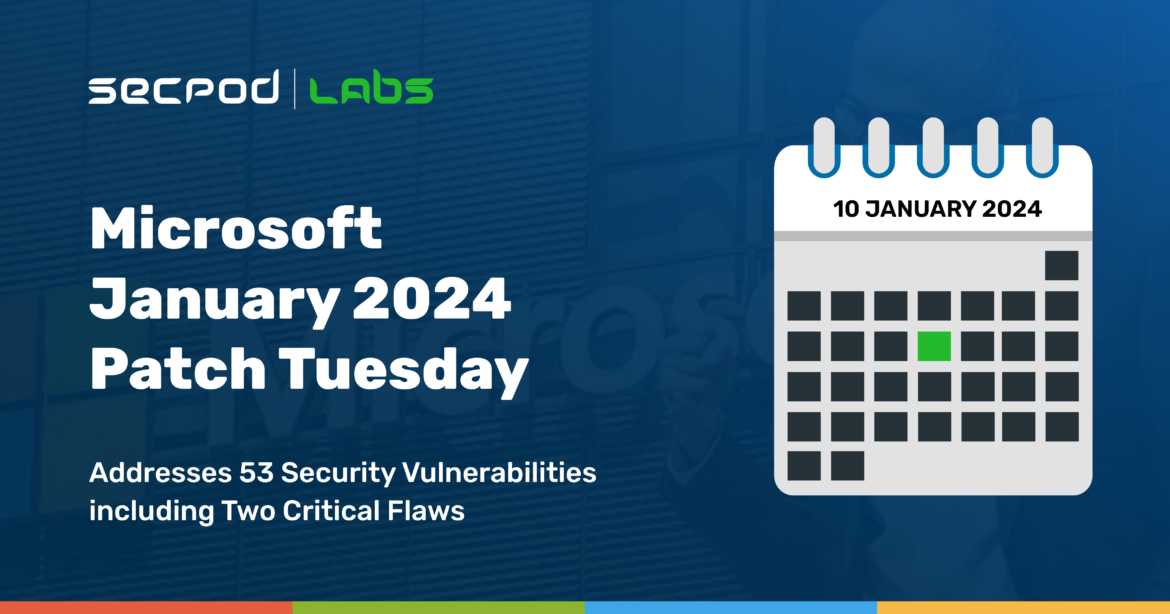
53 Vulnerabilities (2 Critical) Fixed in Microsoft’s January 2024 Patch Tuesday
Cyber Security Blogs The second week of the new year has arrived, and with it comes 2024’s first Microsoft Patch Tuesday. This time around, Microsoft has fixed 53 vulnerabilities, including 2 critical ones. Perhaps as a new year’s gift to patch writers, there have been no zero days reported (that we know of), and none
- Published in RSS blog posts
Halara looked into the breach after a hacker released 950,000 people’s data
Cyber Security Blogs After the purported data of nearly 950,000 customers was disclosed on a hacking forum, well-known athleisure clothing company Halara launched an investigation into a potential data breach. After being established in 2020, the Hong Kong company gained enormous popularity on TikTok thanks to the numerous videos it posted advertising its apparel. According
- Published in RSS blog posts
For breaching 60 firms, a ShinyHunters member receives a 3-year prison sentence
Cyber Security Blogs Sebastien Raoult of ShinyHunters was ordered to pay $5,000,000. The U.S. District Court in Seattle sentenced Raoult to three years in prison. Raoult had previously admitted guilt in September 2023 to conspiring to commit wire fraud and aggravated identity theft, for which he could have received a maximum sentence of 27 years
- Published in RSS blog posts
Proactive vs. Reactive: Safeguarding Your Digital Fortress with Protegent Antivirus
Cyber Security Blogs In the fast-paced digital landscape, the battle against cyber threats is an ongoing saga. In a world where businesses and individuals heavily depend on technology for diverse aspects of their lives, it is paramount to grasp the risks linked with cyber threats and adopt proactive measures to shield our digital assets. As
- Published in RSS blog posts
UAC-0050 Attack Detection: Hackers Are Armed with Remcos RAT, Quasar RAT, and Remote Utilities to Target Ukraine Once Again
Cyber Security Blogs At the end of 2023, the nefarious UAC-0050 group loomed in the cyber threat arena, targeting Ukraine using Remcos RAT, a common malware from the group’s offensive toolkit. In the first decade of January 2024, UAC-0050 reemerges to strike again, exploiting Remcos RAT, Quasar RAT, and Remote Utilities. UAC-0050 Offensive Activity Overview
- Published in RSS blog posts
CVE-2023-36025 Exploited for Defense Evasion in Phemedrone Stealer Campaign
Cyber Security BlogsThis blog delves into the Phemedrone Stealer campaign’s exploitation of CVE-2023-36025, the Windows Defender SmartScreen Bypass vulnerability, for its defense evasion and investigates the malware’s payload. Read More
- Published in RSS blog posts