Disclaimer:
The RSS blog posts featured on our website are external articles imported through an automated process. We do not verify the accuracy or completeness of the information contained in these posts. The views and opinions expressed in these articles are those of the authors and do not necessarily reflect our own. We are not responsible for any errors, omissions, or misstatements that may appear in these posts. Readers are advised to independently verify any information before relying on it.
If you find any information that you believe to be dangerous, harmful, inaccurate, or in violation of GDPR or other laws, please contact us immediately, and we will take steps to remove it.
Beyond Convenience: Can You Trust Your Smart Home?
Cyber Security Blogs You settle into your cozy armchair for a movie night, your smart lights dimming automatically as you fire up the projector. As the opening credits roll, you reach for your phone to order popcorn, only to be met with a chilling notification: “Unauthorized access detected on your smart kitchen appliances.” Your blood
- Published in RSS blog posts
For Patch Tuesday, 48 updates, no zero-day flaws
Cyber Security Blogs Microsoft has eased us into the new new year with just 48 updates for the Windows, Office and .NET platforms. There were no zero-days for January, and no reports of publicly exposed vulnerabilities or exploited security issues. Developers of complex, line-of-business applications might need to pay particular attention to how Microsoft has
- Published in RSS blog posts
Sneaky Azorult Back in Action and Goes Undetected
Cyber Security Blogs Cyble Research and Intelligence Labs examines the recent infection chain employed in the latest Azorult malware campaign The post Sneaky Azorult Back in Action and Goes Undetected appeared first on Cyble. Read More
- Published in RSS blog posts
What is threat management?
Cyber Security Blogs What is Threat Management? Threat Management is a comprehensive procedure that identifies, prevents, and responds to cyber threats. A robust threat management process is crucial in minimizing the risk of cyberattacks. By proactively addressing potential threats, organizations can enhance their cybersecurity posture and fortify their defenses against evolving digital risks. How does
- Published in RSS blog posts
6,200+ WordPress Sites with POPUP BUILDER Plugin Infected by New Balada
Cyber Security Blogs Over 6,700 WordPress websites use a vulnerable version of the Popup Builder plugin to build custom popups for marketing, informational, and functional purposes, inadvertently fell victim to the insidious Balada Injector malware. This coordinated attack, discovered by security researchers at Dr. Web, not only exploited known flaws in WordPress themes and add-ons
- Published in RSS blog posts
The state of the cyber security talent shortage
Cyber Security Blogs EXECUTIVE SUMMARY: With over 4 million unfilled cyber security jobs globally, organizations are not only wrestling with a severe shortage of cyber security workers, but also a paucity of those who possess essential skills. The talent shortage has led to higher workloads for existing cyber security staff, resulting in untenable levels of
- Published in RSS blog posts
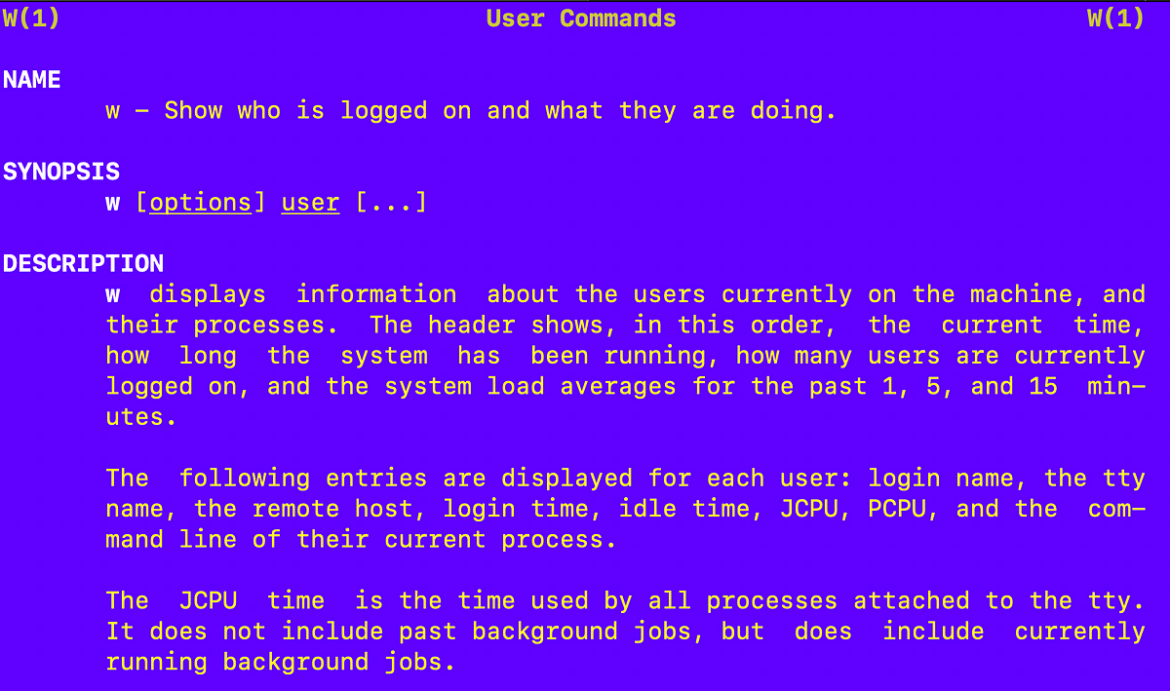
Extraneous Connections After Getting Disconnected From a Linux SSH Connection
Cyber Security Blogs If you get disconnected — run this command to make sure you only have the expected connections Read More
- Published in RSS blog posts
AI and privacy – Addressing the issues and challenges
Cyber Security Blogs The content of this post is solely the responsibility of the author. AT&T does not adopt or endorse any of the views, positions, or information provided by the author in this article. Artificial intelligence (AI) has seamlessly woven itself into the fabric of our digital landscape, revolutionizing industries from healthcare to finance.
- Published in RSS blog posts
An Introduction to AWS Security
Cyber Security BlogsCloud providers are becoming a core part of IT infrastructure. Amazon Web Services (AWS), the world’s biggest cloud provider, is used by millions of organizations worldwide and is commonly used to run sensitive and mission-critical workloads. This makes it critical for IT and security professionals to understand the basics of AWS security and
- Published in RSS blog posts
Medusa group steps up ransomware activities
Cyber Security Blogs A fast rising ransomware outfit is escalating its activities and has launched a new blog offering victims a variety of payoff options, according to a report released Thursday by Palo Alto Networks’ Unit 42. The new Medusa Blog is used by the group to post stolen data with the threat of exposing
- Published in RSS blog posts