Disclaimer:
The RSS blog posts featured on our website are external articles imported through an automated process. We do not verify the accuracy or completeness of the information contained in these posts. The views and opinions expressed in these articles are those of the authors and do not necessarily reflect our own. We are not responsible for any errors, omissions, or misstatements that may appear in these posts. Readers are advised to independently verify any information before relying on it.
If you find any information that you believe to be dangerous, harmful, inaccurate, or in violation of GDPR or other laws, please contact us immediately, and we will take steps to remove it.
Beyond Breach: The Aftermath of a Cyberattack
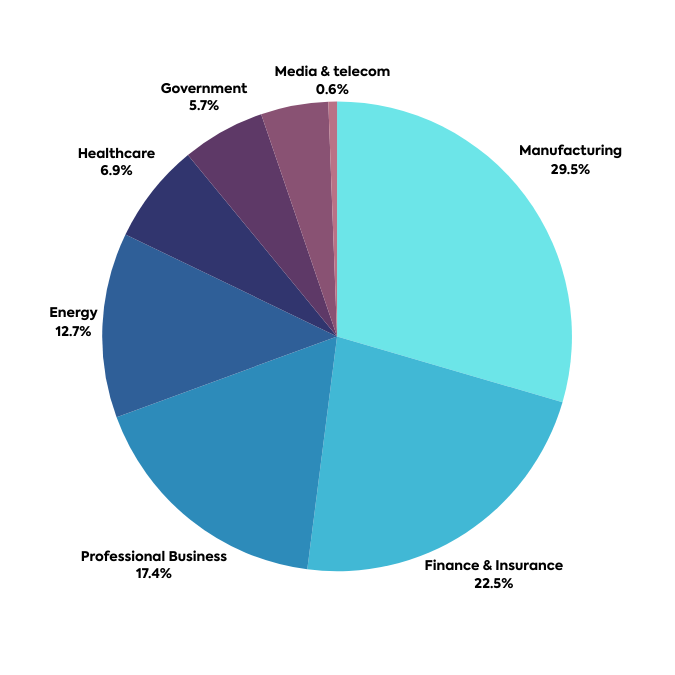
Cyber Security Blogs Cyberattacks are no longer an occasional headline; they’ve become a grim reality. In 2023 alone, a staggering 236.1 million ransomware attacks occurred globally in just the first half of the year, according to Cybersecurity Ventures. That translates to a staggering one attack every 1.4 seconds. While the immediate costs of data breaches,
- Published in RSS blog posts
Kansas State University suffered a serious cybersecurity incident
Cyber Security BlogsKansas State University (K-State) suffered a cybersecurity incident that has disrupted part of its network and services. Kansas State University (K-State) suffered a cybersecurity incident that impacted a portion of its network and services. On January, 16, 2023, the University K-State announced it was experiencing a disruption to certain network systems, including VPN,
- Published in RSS blog posts
Experts Urge Clearer Direction in South Africa’s Cyber Strategy
Cyber Security BlogsSouth Africa’s cyber defenses have been lacking direction and resources for too long, researchers from the Carnegie Endowment for International Peace argued Read More
- Published in RSS blog posts
AI misinformation, world’s biggest short-term threat, says WEF
Cyber Security Blogs EXECUTIVE SUMMARY: In 2024, 70 nations, comprised of over 3.7 billion people (nearly half of the world’s population) will hold presidential or legislative elections. The World Economic Forum’s 2024 Global Threats Report, published just ahead of the group’s annual event that takes place this week, highlighted misinformation and disinformation as the #1
- Published in RSS blog posts
From Email to RAT: Deciphering a VB Script-Driven Campaign
Cyber Security Blogs Authored by Preksha Saxena and Yashvi Shah McAfee Labs has been tracking a sophisticated VBS campaign characterized by obfuscated Visual Basic Scripting (VBS). Initially delivering the AgentTesla malware, the campaign has evolved into a multi-faceted threat, employing VBS scripts as a versatile delivery mechanism. Notably, this campaign extends beyond AgentTesla, now distributing
- Published in RSS blog posts
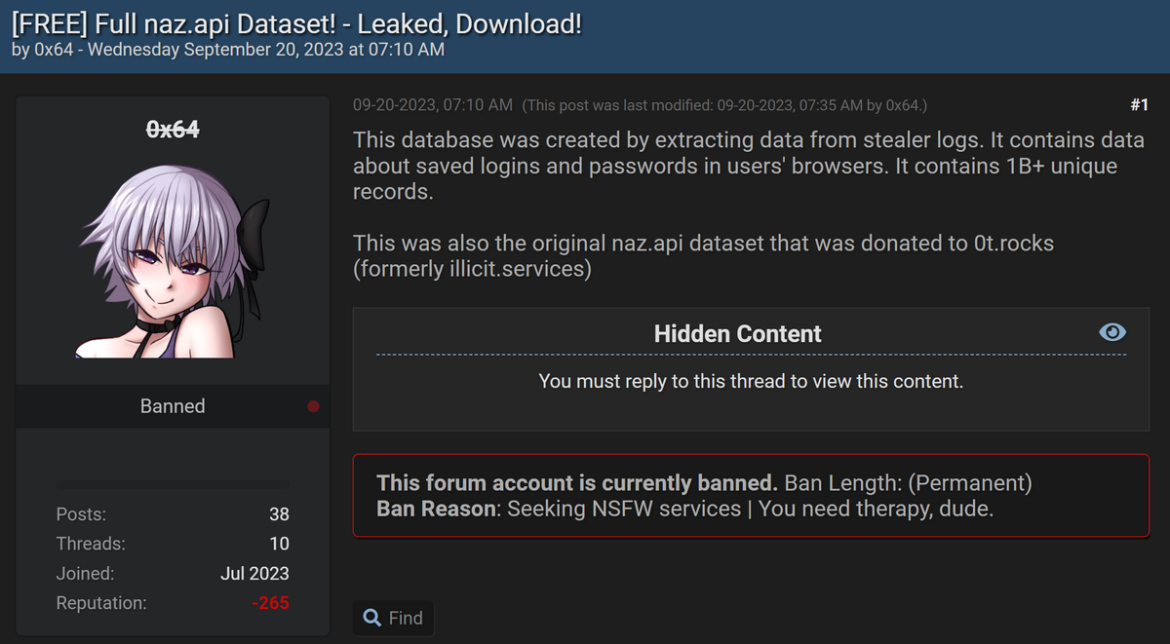
Inside the Massive Naz.API Credential Stuffing List
Cyber Security Blogs It feels like not a week goes by without someone sending me yet another credential stuffing list. It’s usually something to the effect of “hey, have you seen the Spotify breach”, to which I politely reply with a link to my old No, Spotify Wasn’t Hacked blog post (it’s just the output
- Published in RSS blog posts
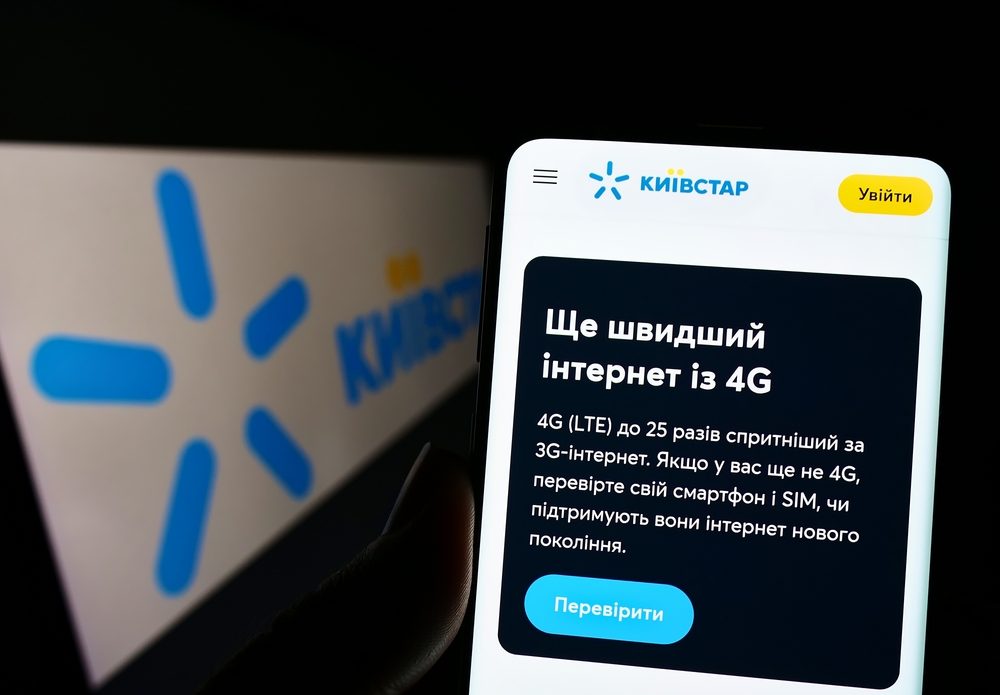
Veon Estimates Nearly $95 Million Revenue Loss Post Kyivstar Cyberattack
Cyber Security Blogs Veon, the parent company for Kyivstar, Ukraine’s top mobile operator, recently outlined the financial impact of the Kyivstar cyberattack in December. The breach is anticipated to have caused a substantial revenue shortfall for the 2024 fiscal year, estimated at around 3.6 billion Ukrainian hryvnias, or nearly $95 million. Kyivstar cyberattack resulted in
- Published in RSS blog posts
Hunters International Targets Gallup-McKinley County Schools as Their Latest Victim
Cyber Security Blogs The Hunters International ransomware group has announced its latest conquest, asserting that Gallup-McKinley County Schools in New Mexico have fallen victim to their cyber onslaught. The Gallup-McKinley County Schools cyberattack claim, however, lacks critical details such as the nature of data compromise, the extent of the breach, or the motives driving the
- Published in RSS blog posts
Out with the old and in with the improved: MFA needs a revamp
Cyber Security Blogs From AI to ZTA (zero-trust architecture), the technology responsible for protecting your company’s data has evolved immensely. Despite the advances, cybercriminals repeatedly find new and creative ways to gain access to sensitive information. This can result in devastating consequences, making it key for leaders in the industry to proactively think about threats.
- Published in RSS blog posts
Attackers Could Eavesdrop on AI Conversations on Apple, AMD, Imagination and Qualcomm GPUs
Cyber Security BlogsSecurity researchers from Trail of Bits identified a GPU memory vulnerability they called LeftoverLocals. Some affected GPU vendors have issued fixes. Read More
- Published in RSS blog posts